Radikant-TLS-C
Introduction
Radikant TLS is a light weight TLS (Transport Layer Security) protocol 1.3 client & server library written in C. Supporting botu client and server mode in 1.2 and 1.3 turned into self inflicted pain. Modern servers support tls 1.3 therefore 1.2 support is completely dropped.
This library relies on Radikant Crypto for all its underlying cryptographic primitivees, utilizes Radikant Socket for socket managment and Radikant Cert for certificate management such as x509/pem etc..
This library is a proof-of-concept that TLS statemachine is doable from scratch, however currently it is insecure currently since its corner stone Radikant Crypto is currently insecure (leaks memory, secrets and non-constant time). It is a demonstration/experiment how to split up TLS smaller managable modules.
Currently in client mode the client skips verifying the server identity because PKI and root Certificate validation is not implemented in the Certificate module.
TLS 1.3
Cipher Suites
AES256 GCM SHA384
Tx
AES128 CCM SHA256
Tx
AES128
CCM 8
SHA256
Txt
AES128
CCM
SHA256
Tx
CHACHA20 POLY1305 SHA256
tx
Key Generation
X25519
Tx
X448
Tx
P-256
Txt
P-384
Tx
P-521
tx
int main(int argc, char *argv[]) {
const char *hostname = "google.com";
const char *port = "443"; // Standard HTTPS port
int sock_fd = tcp_connect(hostname, port);
tls_context *ctx = tls_context_new(TLS_MODE_CLIENT);
tls_context_set_socket(ctx, sock_fd);
tls_connect(ctx, hostname);
tls_context_free(ctx);
return 0;
}
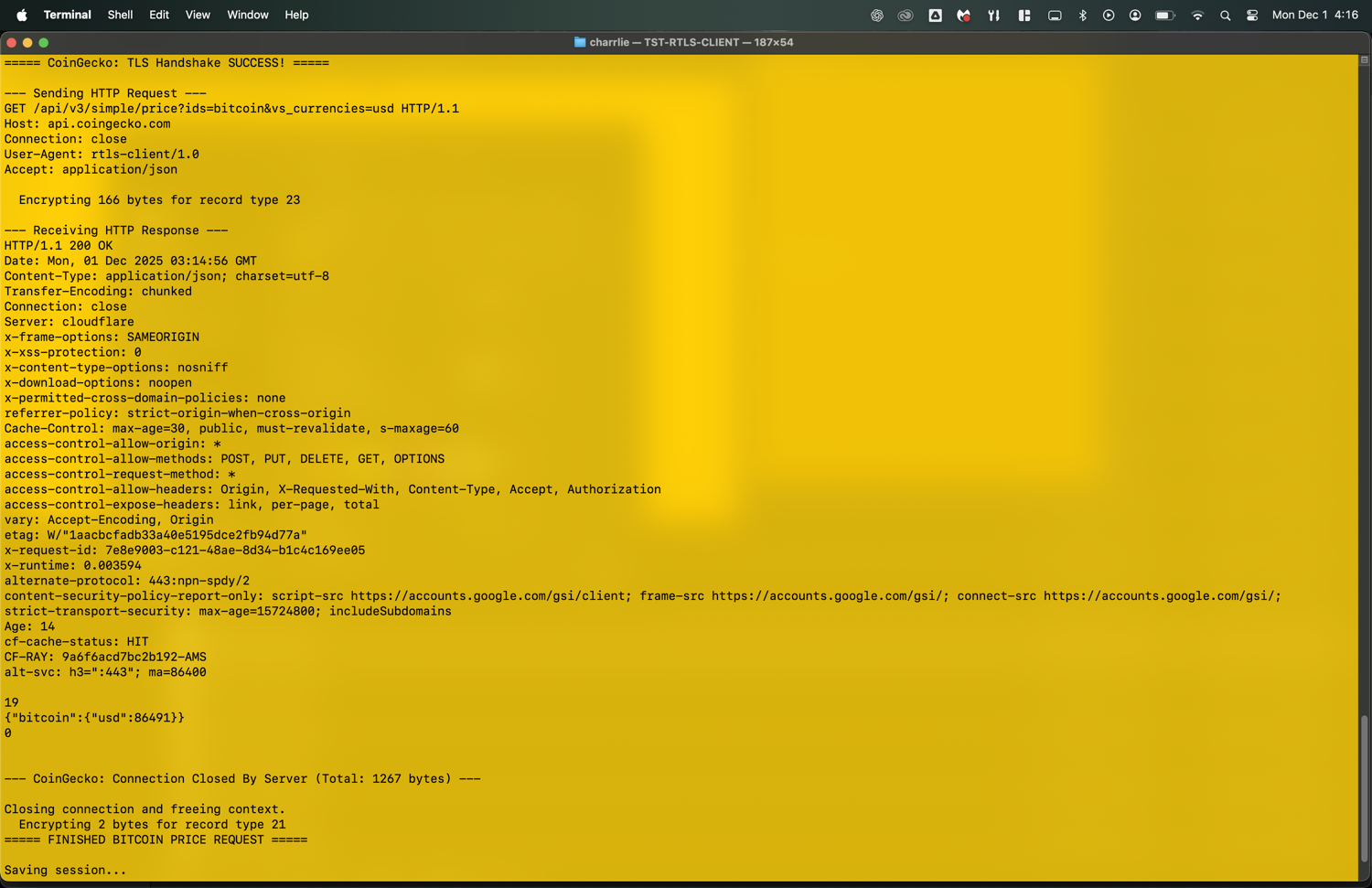
<HTML><HEAD><meta http-equiv="content-type" content="text/html;charset=utf-8"> <TITLE>301 Moved</TITLE></HEAD><BODY> <H1>301 Moved</H1> The document has moved <A HREF="https://www.google.com/">here</A>. </BODY></HTML>Google: Connection Closed By Server (Total: 851 bytes) Closing connection and freeing context. Encrypting 2 bytes for record type 21 ===== FINISHED GOOGLE.COM REQUEST =====